Table of Contents
Malware Warning!
The impact of malware targeting the BIOS can extend far beyond the individual user; it affects industries, economies, and even national security. With the rise of remote work and online gaming, the potential for widespread disruption increases significantly. Businesses may face operational halts, and data breaches could lead to legal repercussions. The financial costs of recovering from a BIOS-level attack can be crippling, prompting some companies to rethink their entire cybersecurity strategies.
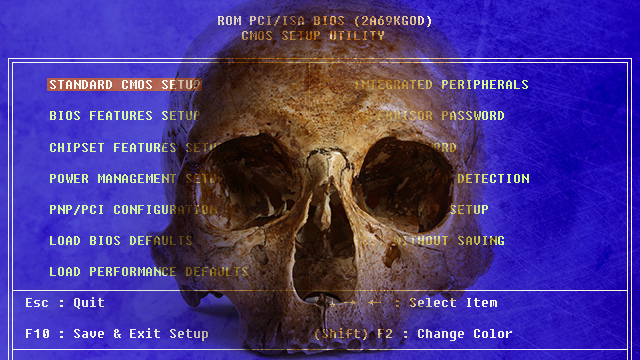
A New Kind Of Malware
There’s a brand-new kind of malware affecting mostly high-end gaming machines running Windows. This malware is not the kind you can just clean off your hard drive! No, it gets installed into your BIOS chip on the motherboard! Once it gets installed, this malware prevents your computer from booting up at all! It turns your motherboard into a useless paperweight! In recent times, the sophistication and stealth of such malware have increased, making it a real nightmare for users.
I’ve had two clients so far who asked me to repair their systems, but I had to tell them I couldn’t repair the motherboards because of the BIOS. The implications of this are substantial, especially as more users rely heavily on their machines for both work and leisure.
Think This Is Just A Bad Dream?
In case you think this is too “far-fetched” to be true, please take a look at this article on the “badBIOS” malware discovered by Ruiu, a computer security expert.
A Wake-Up Call
This malware threat is a wake-up call for all users, prompting a need for ongoing dialogue within the tech community. We must continue to push for innovations that enhance security and hold manufacturers accountable. Together, we can mitigate the risks posed by this evolving threat and ensure that our technology remains a source of empowerment rather than vulnerability. The time to act is now. Users must demand better security features in their devices and advocate for industry standards that prioritize protection against BIOS-level malware. Let us not wait until we become victims ourselves.
Always be aware of malware symptoms, keep your software up to date, and engage with your community to raise awareness of malware risks. This collective effort can foster a safer digital environment for all users, ultimately minimizing the risks posed by infections targeting critical hardware components such as the BIOS. Remember, staying informed is your best defense.
As we continue to navigate the evolving technological landscape, vigilance and education will play significant roles in defending against the next wave of malware threats. It’s essential not only to protect your own devices but also to advocate for industry-wide changes that prioritize consumer safety and hardware design integrity.
Preventative Measures
In light of the increasing threat of BIOS malware, it’s crucial for users to adopt preventative measures. Regularly updating your operating system and firmware can also reduce vulnerability. Moreover, participating in community discussions about hardware security can lead to more awareness and shared solutions. Engaging with open-source projects and contributing to discussions can help develop more robust defenses against these types of attacks. Cybersecurity is a collective responsibility, and every action counts in the fight against malware.
To better understand how damaging this malware can be, consider the examples of recent attacks reported in various tech forums. Users have shared their experiences of waking up to find their systems unresponsive and their data inaccessible. Many have expressed frustration and helplessness due to the lack of available solutions. Additionally, the broader repercussions of such malware attacks can lead to significant financial losses for gaming companies and developers, as players may be unable to play their games or access their accounts.
This kind of malware can be used against ANY operating system! It can be used against any version of Windows, macOS, or Linux! The only hope of dealing successfully with this problem is for a standardized open-source version of BIOS to become commonplace and be easily reflashed by most home PC users, even after infection. This is unlikely to happen any time soon due to financial concerns.
One possible solution is to make the BIOS chip permanently “unwritable” by ensuring it is a “burned” ROM rather than a rewritable one, and by using only the “minimum” instructions to make the PC motherboard “bootable”.
If you are concerned about malware threats, here are some proactive steps you can take. First, ensure you have a reliable antivirus program that is frequently updated. Second, regularly back up your data to an external drive or cloud service. This way, in the unfortunate event of a malware infection, you can restore your system without losing essential files. Additionally, consider using virtual machines for software testing or internet browsing, as this can add a layer of security by isolating potential threats. Educating yourself on the latest cybersecurity trends and threats can empower you to make informed decisions about your technology usage.
This situation is extremely serious and very troubling! What can you do to help? Try using Linux! Even though it is possible to get a Linux machine infected with this kind of malware, it is far less likely to happen on Linux because of how Linux works!
You can also learn about open-source BIOS projects like “CoreBoot” and others. You can talk with people at various PC and laptop manufacturers and let them know you would like to purchase hardware that has already been designed to eliminate the possibility of a BIOS infection! This is something that manufacturers can easily accomplish, and I’m sure that they will listen if enough people request this feature. So get out your phone and let them know what you want!
Please check out our Computer Services!
